Use this guide when Console and the Kubernetes cluster it manages cannot reach the public internet. Air-gapped deployments need more preparation because Console may otherwise downloadDocumentation Index
Fetch the complete documentation index at: https://docs.risingwave.com/llms.txt
Use this file to discover all available pages before exploring further.
risectl binaries, pull public images, or fetch Helm charts during environment installation.
Checklist
Prepare these artifacts before starting Console:- Console image, usually an
-airgaptag if you need pre-cachedrisectlbinaries. - Signed RisingWave license key.
- Private Docker registry reachable from the Kubernetes nodes.
- Mirrored images for Console-managed components.
- cert-manager and RisingWave Operator Helm chart archives.
- Any RisingWave database images you plan to deploy.
- Optional Grafana dashboards if your workflow installs Grafana.
Start Console without internet access
Set:Mirror images
Mirror the images used by Console-managed infrastructure into your private registry. The Console repository includes helper scripts for testing and mirroring:Configure the private registry in Console
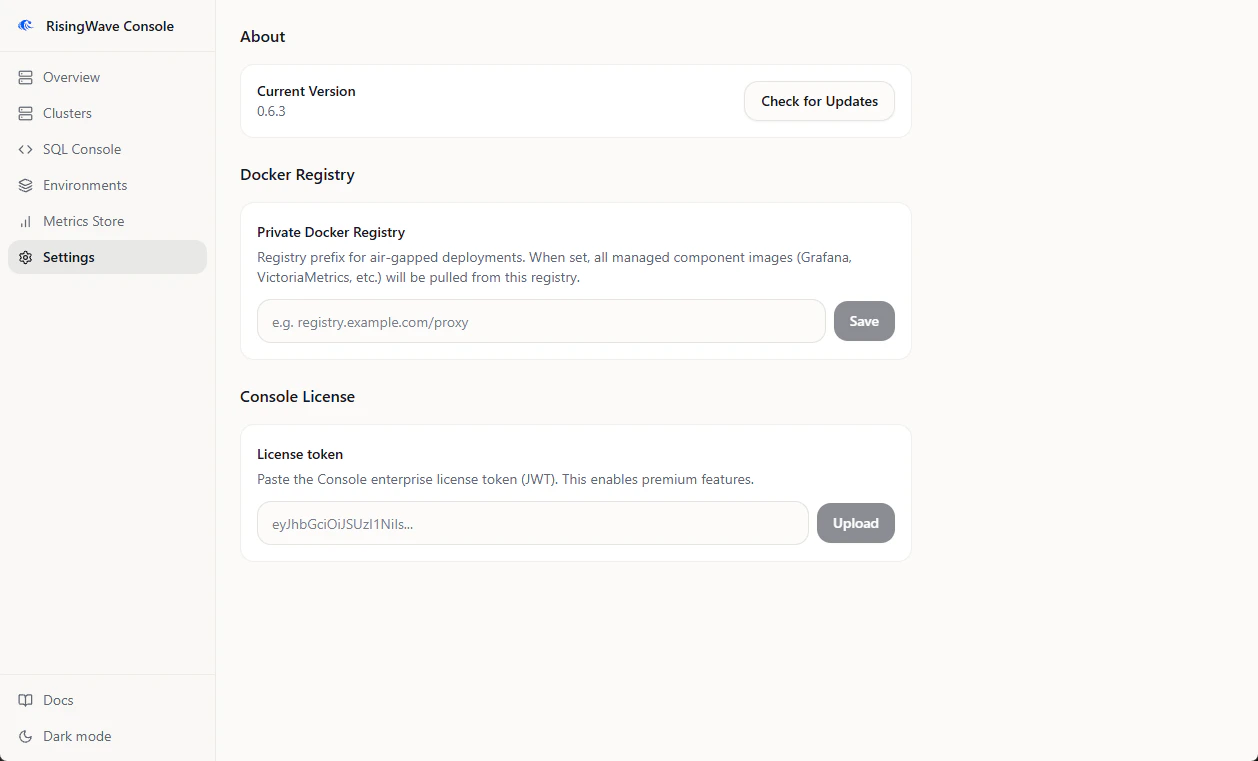
- Open Settings.
- Find Docker Registry.
- Set Private Docker Registry to the same prefix used when mirroring images, for example
registry.example.com/proxy. - Click Save.
Provide Helm charts
In air-gapped mode, Console cannot fetch missing Helm charts. Put chart archives in the directory configured byRCONSOLE_HELM_CHART_DIR, or upload them from the relevant install workflow when the UI prompts for a chart archive.
The default chart directory is:
.tgz Helm chart files.
Provide risectl binaries
Console usesrisectl for cluster operations. In a connected deployment, it can download the needed version. In an air-gapped deployment, use an air-gap Console image with the needed versions pre-cached, or mount binaries under:
Validate the setup
Before creating production clusters:- Confirm Console starts with
RCONSOLE_NOINTERNET=true. - Confirm Settings shows the private Docker registry value.
- Create an environment with the same components you plan to use in production.
- Watch the install logs for image pull or chart lookup errors.
- Run the environment acceptance test.
Troubleshooting
| Symptom | Check |
|---|---|
helm chart not available for air-gapped install | Upload the required chart archive or mount it under RCONSOLE_HELM_CHART_DIR. |
Kubernetes reports ImagePullBackOff | Confirm the private registry prefix, mirrored image names, image tags, and node registry credentials. |
risectl command fails because the binary is missing | Mount the expected risectl version under RCONSOLE_RISECTLDIR, or use an air-gap image with that version included. |
| Private HTTP registry cannot be pulled by containerd | Configure the Kubernetes nodes to trust the registry as an insecure registry, or serve it with TLS. |