RisingWave Cloud exposes a set of environment-specific metadata values for each project. These values are required when setting up cross-account access (IAM role assume) and PrivateLink connections. All values are read-only and are generated automatically when a project is created.Documentation Index
Fetch the complete documentation index at: https://docs.risingwave.com/llms.txt
Use this file to discover all available pages before exploring further.
Where to find cloud metadata
In the RisingWave Cloud Console, go to your project and click Connection in the left sidebar. Then select the Cloud Meta tab.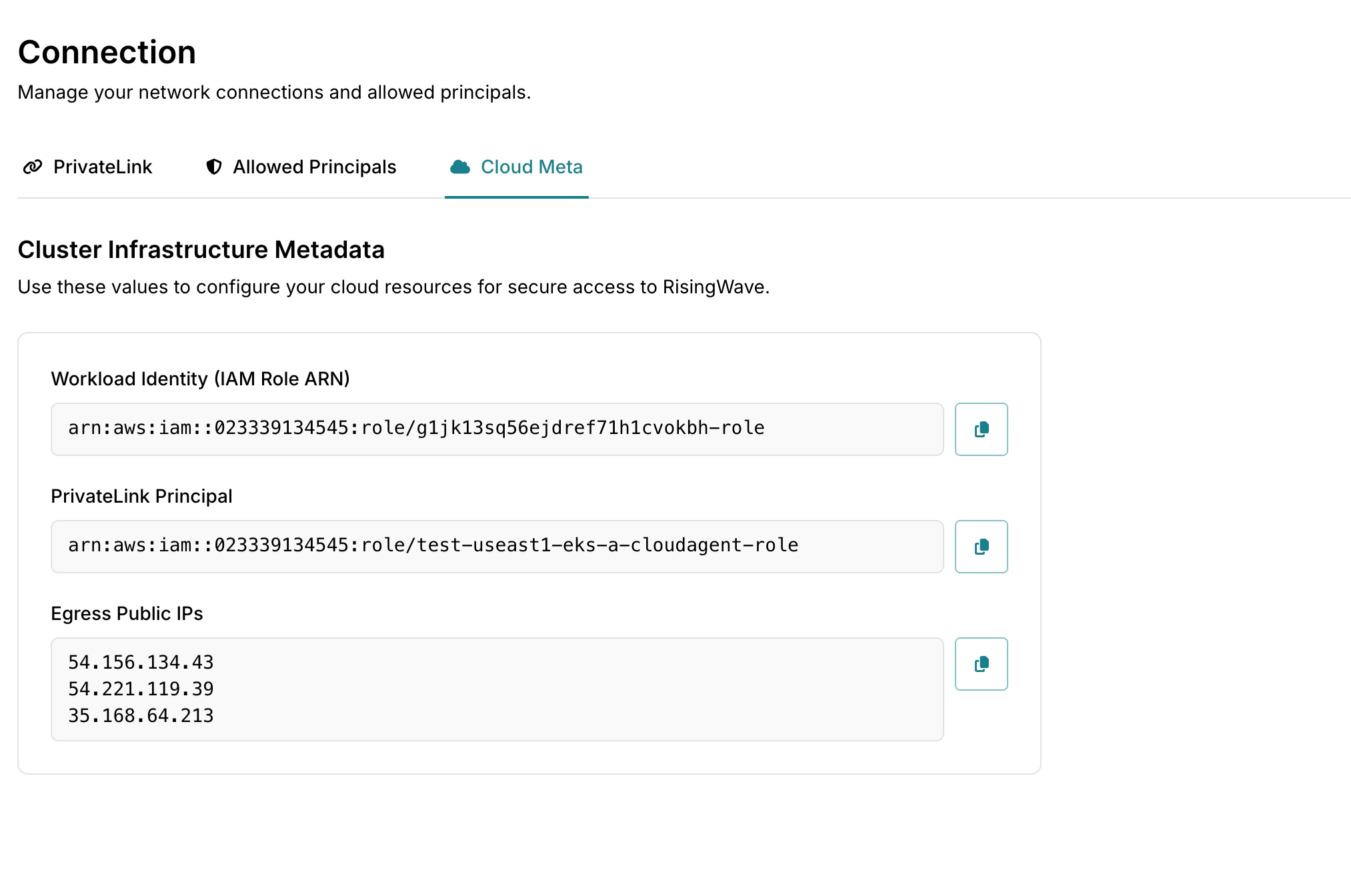
Cloud metadata is only available for projects on the Standard plan or above.
Metadata fields
Workload Identity (IAM Role ARN)
| Field | Example value |
|---|---|
| Workload Identity (IAM Role ARN) | arn:aws:iam::023339134545:role/g1jk13sq56ejdref71h1cvokbh-role |
PrivateLink Principal
| Field | Example value |
|---|---|
| PrivateLink Principal | arn:aws:iam::023339134545:role/test-useast1-eks-a-cloudagent-role |
Egress public IPs
| Field | Example value |
|---|---|
| Egress public IPs | 203.0.113.10, 203.0.113.11 |
Cloud metadata by platform
| Metadata field | AWS | GCP | Azure |
|---|---|---|---|
| Workload Identity (IAM Role ARN) | ✅ | ✅ (service account email) | ✅ (managed identity resource ID) |
| PrivateLink Principal | ✅ (AWS account ARN) | ✅ (GCP project number) | ✅ (Azure subscription ID) |
| Egress public IPs | ✅ | ✅ | ✅ |
GCP and Azure metadata field names differ from the AWS equivalents. The Console labels each field for the platform of your project.
Next steps
- Set up IAM role assume — use the IAM role ARN to grant RisingWave Cloud cross-account S3 access.
- Configure PrivateLink — use the PrivateLink Principal when setting up your endpoint service’s allowed principals.